Aria stories - Page 90
Aria is where cutting‑edge technology, security, and AI‑driven innovation intersect. The stories tagged here span everything from next‑gen cloud and data platforms to ransomware trends, smart infrastructure, and the fast‑evolving world of generative and agentic AI. If you want to understand how tools like AI copilots, LLMs, and real‑time analytics are reshaping everything from finance to healthcare to manufacturing, this is your starting point.
Dive into in‑depth coverage of cybersecurity – botnets, ransomware variants, mobile malware, zero‑day exploits, and the shift to continuous, intelligence‑led defence. Explore how data centres, networks, and observability platforms are being redesigned for AI workloads, sustainability, and hybrid cloud. Follow the rise of AI in everyday products too, from wearables and smart home devices to vehicles, retail experiences, and next‑gen collaboration tools.
Aria isn’t just about the technology itself, but about its impact: on regulation, trust, jobs, skills, and digital resilience. Here you’ll find expert commentary, major vendor announcements, case studies, and long‑form explainers that help you connect the dots between infrastructure, security, AI, and real business outcomes. If you’re responsible for strategy, architecture, risk, or innovation, the Aria tag will keep you ahead of what’s coming next.

Hackers run circles around Samsung's iris scanner security
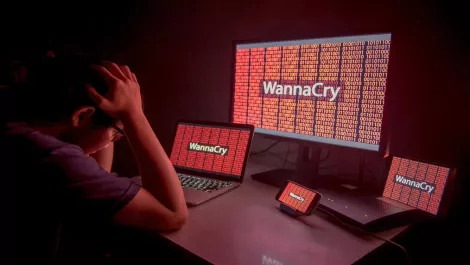
Digital Shadows on Wannacry: An analysis of competing hypotheses

Avoiding pitfalls in IoT integration - Gartner
Mid-market CRM software Sugar announces update to version 7.9

A look at the evolution of the Nemucod malware

Veeam debuts 'partner-centric' offerings, upgrades – and new partner program

How to protect your organisation from WannaCry ransomware

In-depth: Security experts explain the WannaCry ransomware's world domination

The rise of ransomware in Southeast Asia

What we can learn from the Google Docs hack

What makes Locky and Cerber ransomware so good - and what about CradleCore?

What makes the Cerber ransomware so agile?

Bitdefender creates decryption tool for Bart ransomware victims

No favourites here: What makes up the art of cybersecurity warfare

Kazuar trojan hijacks Microsoft .NET framework to conduct espionage attacks

WatchGuard report: 30% of all malware isn't caught by legacy AV

Global warning as spam attacks target stock market manipulation

May the 4th be with you: Star Wars tech that actually exists
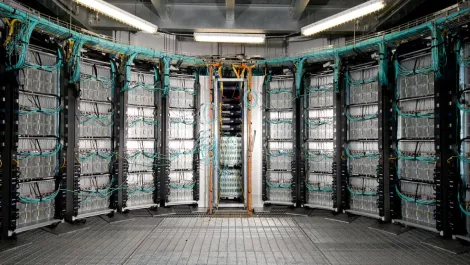
Adiabatic and evaporative cooling techniques deliver big data center savings
